Is there a serious difference to order a PDF, or hard copy of a CompTIA 220-901 dumps certificate? The CompTIA A+ Certification Exam (220-901) exam is a 296 questions assessment in pass4itsure that is associated with the CompTIA A+ certification. Most important CompTIA 220-901 dumps exam study guide actual questions video training are the best materials. “CompTIA A+ Certification Exam” is the exam name of Pass4itsure CompTIA 220-901 dumps test which designed to help candidates prepare for and pass the CompTIA 220-901 exam. We are more than happy to help our IT students with every single help we can assist them with theirCompTIA A+ Certification https://www.pass4itsure.com/220-901.html dumps exam problems. This is how we make so many IT students in this field.
[Latest CompTIA 220-901 Dumps Certification Center From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWU3RVZHZ5YWNXQTQ
[Latest Cisco 200-150 Dumps Certification Center From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWTi1YUDlKM3U3R1U
Up to the immediate present CompTIA 220-901 dumps exam cram:
QUESTION 52
Which of the following is a type of fiber connector?
A. RJ-11
B. F-connector
C. BNC
D. ST
220-901 exam Correct Answer: D
QUESTION 53
Joe, a user, receives a wireless router from his ISP with a pre-set password and configuration. He can connect to the router fine via Ethernet but cannot see the wireless signal on any of his devices. The LEDs on the router indicate that a wireless signal is broadcasting. Which of the following settings on the router does Joe need to adjust to enable the devices to see the wireless signal?
A. DHCP
B. IPv6
C. DMZ
D. SSID
Correct Answer: D
QUESTION 54
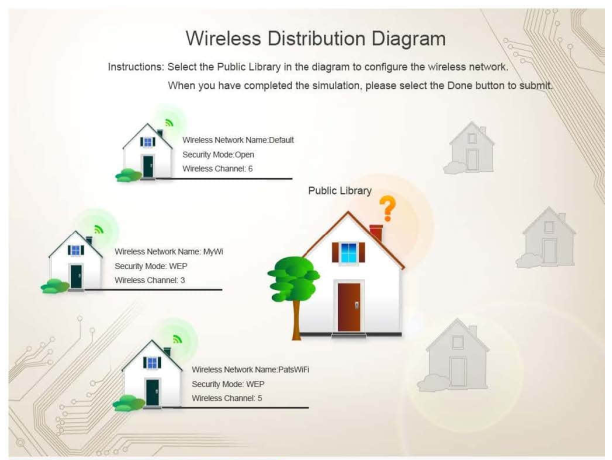
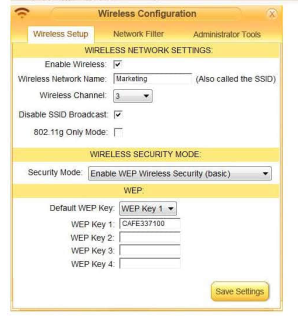
Ann, a local librarian, has had a previously used wireless access point donated to her. She has instructed you to configure this new wireless access point for her public library. Ann plans to allow anyone to connect to the access point without having to ask her configuration information. Additionally, Ann knows that her neighbors have wireless networks and wants to ensure that her network does not interfered with the other networks. Ann has provided you with the following information. Wireless Name: Library New Router Password: SecureSI Instructions: Select the Public Library in the diagram to configure the wireless network. Once the wireless network tabs are configured, select the save button. When you have completed the simulation, please select the Done button to submit.

220-901 dumps Correct Answer:
QUESTION 55
A user reports an inkjet printer is constantly feeding two sheets of paper for every page printed. Which of the following is the MOST likely reason?
A. Poor paper quality
B. Incorrect paper size
C. Defective duplexer
D. Worn feed rollers
Correct Answer: D
QUESTION 56
A technician needs to boot a PC from a USB drive. Which of the following settings should be disabled to accomplish this task?
A. Fast Boot
B. UEFI Admin Password
C. Secure Boot
D. Legacy Boot
220-901 pdf Correct Answer: C
QUESTION 57
A technician is tasked with selecting components to build a computer that will be used for computer-aided drafting and computer aided modeling. Which of the following components are the BEST choices? {Select TWO).
A. Triple channel memory
B. MIDI sound card
C. Socket 1156 motherboard
D. Onboard graphics
E. Socket 1366 CPU
Correct Answer: AE
QUESTION 58
Which of the following expansion slots uses a serial connection?
A. PCI
B. PCI-X
C. PCIe
D. AGP
220-901 vce Correct Answer: C
QUESTION 59
Which of the following expansion slots is MOST commonly used for high-end video cards?
A. PCI
B. PCIe
C. CNR
D. AGP
Correct Answer: B
QUESTION 60
A user, Ann, is preparing to travel abroad and wants to ensure that her laptop will work properly. Which of the following components of the laptop should be verified FIRST to ensure power compatibility before traveling?
A. Wall adapter
B. Battery
C. Power supply
D. Digitizer
220-901 exam Correct Answer: A
QUESTION 61
Ann, a user, boots her laptop and notices the screen flashes then turns black. It was working during her presentation yesterday. Which of the following troubleshooting steps should be completed?
A. Use a multimeter to test voltage.
B. Replace the laptop with a new one.
C. Replace the battery.
D. Connect an external display device.
Correct Answer: D
QUESTION 62
Which of the following wireless technologies is LEAST likely to be intercepted by a third party?
A. NFC
B. Bluetooth
C. WiFi
D. Cellular
220-901 dumps Correct Answer: A
QUESTION 63
A user reports that the mouse is not working properly. The technician notices on the user\’s workstation that the mouse cursor spins for several minutes before the technician can use the mouse. Which of the following is the cause of the issue?
A. Failed Operating System
B. Faulty mouse
C. Faulty CPU
D. Not enough memory
Correct Answer: D
QUESTION 64
Jenny is the project manager of the NHJ Project for her company. She has identified several positive risk events within the project and she thinks these events can save the project time and money. You, a new team member wants to know that how many risk responses are available for a positive risk event. What will Jenny reply to you?
A. Four
B. Seven
C. Acceptance is the only risk response for positive risk events.
D. Three
220-901 pdf Correct Answer: A
QUESTION 65
Wendy is about to perform qualitative risk analysis on the identified risks within her project. Which one of the following will NOT help Wendy to perform this project management activity?
A. Stakeholder register
B. Risk register
C. Project scope statement
D. Risk management plan
Correct Answer: A
QUESTION 66
Which of the following roles is responsible for review and risk analysis of all contracts on a regular basis?
A. The Supplier Manager
B. The IT Service Continuity Manager
C. The Service Catalogue Manager
D. The Configuration Manager
220-901 vce Correct Answer: A
QUESTION 67
You are the project manager for the NHH project. You are working with your project team to examine the project from four different defined perspectives to increase the breadth of identified risks by including internally generated risks. What risk identification approach are you using in this example?
A. SWOT analysis
B. Root cause analysis
C. Assumptions analysis
D. Influence diagramming techniques
Correct Answer: A
QUESTION 68
Which of the following are included in Physical Controls? Each correct answer represents a complete solution. Choose all that apply.
A. Locking systems and removing unnecessary floppy or CD-ROM drives
B. Environmental controls
C. Password and resource management
D. Identification and authentication methods
E. Monitoring for intrusion
F. Controlling individual access into the facilityand different departments
220-901 exam Correct Answer: ABEF
QUESTION 69
Which of the following NIST Special Publication documents provides a guideline on network security testing?
A. NIST SP 800-60
B. NIST SP 800-53A
C. NIST SP 800-37
D. NIST SP 800-42
E. NIST SP 800-59
F. NIST SP 800-53
Correct Answer: D
QUESTION 70
Which one of the following is the only output for the qualitative risk analysis process?
A. Project management plan
B. Risk register updates
C. Enterprise environmental factors
D. Organizational process assets
220-901 dumps Correct Answer: B
QUESTION 71
You are the project manager of the GHG project. You are preparing for the quantitative risk analysis process. You are using organizational process assets to help you complete the quantitative risk analysis process. Which one of the following is NOT a valid reason to utilize organizational process assets as a part of the quantitative risk analysis process?
A. You will use organizational process assets for risk databases that may be available from industry sources.
B. You will use organizational process assets for studies of similar projects by risk specialists.
C. You will use organizational process assets to determine costs of all risks events within thecurrent project.
D. You will use organizational process assets for information from prior similar projects.
Correct Answer: C
QUESTION 72
Which of the following objectives are defined by integrity in the C.I.A triad of information security systems? Each correct answer represents a part of the solution. Choose three.
A. It preservesthe internal and external consistency of information.
B. It prevents the unauthorized or unintentional modification of information by the authorized users.
C. It prevents the modification of information by the unauthorized users.
D. It prevents the intentional or unintentional unauthorized disclosure of a message’s contents .
220-901 pdf Correct Answer: ABC
QUESTION 73
You and your project team are just starting the risk identification activities for a project that is scheduled to last for 18 months. Your project team has already identified a long list of risks that need to be analyzed. How often should you and the project team do risk identification?
A. At least once per month
B. Identify risks is an iterative process.
C. It depends on how many risks are initially identified.
D. Several times until the project moves into execution
Correct Answer: B
QUESTION 74
Eric is the project manager of the MTC project for his company. In this project a vendor has offered Eric a sizeable discount on all hardware if his order total for the project is more than $125,000. Right now, Eric is likely to spend $118,000 with vendor. If Eric spends $7,000 his cost savings for the project will be $12,500, but he cannot purchase hardware if he cannot implement the hardware immediately due to organizational policies. Eric consults with Amy and Allen, other project managers in the organization, and asks if she needs any hardware for their projects. Both Amy and Allen need hardware and they agree to purchase the hardware through Eric’s relationship with the vendor. What positive risk response has happened in this instance?
A. Transference
B. Exploiting
C. Sharing
D. Enhancing
220-901 vce Correct Answer: C
QUESTION 75
You work as a project manager for BlueWell Inc. You are preparing to plan risk responses for your project with your team. How many risk response types are available for a negative risk event in the project?
A. Seven
B. Three
C. Four
D. One
Correct Answer: C
QUESTION 76
Sam is the project manager of a construction project in south Florida. This area of the United States is prone to hurricanes during certain parts of the year. As part of the project plan Sam and the project team acknowledge the possibility of hurricanes and the damage the hurricane could have on the project’s deliverables, the schedule of the project, and the overall cost of the project. Once Sam and the project stakeholders acknowledge the risk of the hurricane they go on planning the project as if the risk is not likely to happen. What type of risk response is Sam using?
A. Mitigation
B. Avoidance
C. Passive acceptance
D. Active acceptance
220-901 exam Correct Answer: C
QUESTION 77
Fred is the project manager of the PKL project. He is working with his project team to complete the quantitative risk analysis process as a part of risk management planning. Fred understands that once the quantitative risk analysis process is complete, the process will need to be completed again in at least two other times in the project. When will the quantitative risk analysis process need to be repeated?
A. Quantitative risk analysisprocess will be completed again after the plan risk response planning and as part of procurement.
B. Quantitative risk analysis process will be completed again after the cost managementplanning and as a part of monitoring and controlling.
C. Quantitativerisk analysis process will be completed again after new risks are identified and as part of monitoring and controlling.
D. Quantitative risk analysis process will be completed again after the risk response planning and as a part of monitoring and controlling.
Correct Answer: D
QUESTION 78
You are the project manager for a construction project. The project includes a work that involves very high financial risks. You decide to insure processes so that any ill happening can be compensated. Which type of strategies have you used to deal with the risks involved with that particular work?
A. Transfer
B. Mitigate
C. Accept
D. Avoid
220-901 dumps Correct Answer: A
QUESTION 79
Which of the following are included in Administrative Controls? Each correct answer represents a complete solution. Choose all that apply.
A. Conducting security-awareness training
B. Screening of personnel
C. Monitoring for intrusion
D. Implementing change control procedures
E. Developing policy
Correct Answer: ABDE
QUESTION 80
The Phase 2 of DITSCAP C&A is known as Verification. The goal of this phase is to obtain a fully integrated system for certification testing and accreditation. What are the process activities of this phase? Each correct answer represents a complete solution. Choose all that apply.
A. Configuring refinement of the SSAA
B. Assessment of the Analysis Results
C. System development
D. Certification analysis
E. Registration
220-901 pdf Correct Answer: ABCD
QUESTION 81
You are the project manager for GHY Project and are working to create a risk response for a negative risk. You and the project team have identified the risk that the project may not complete on time, as required by the management, due to the creation of the user guide for the software you’re creating. You have elected to hire an external writer in order to satisfy the requirements and to alleviate the risk event. What type of risk response have you elected to use in this instance?
A. Sharing
B. Avoidance
C. Transference
D. Exploiting
Correct Answer: C
QUESTION 82
You are the project manager of the GHQ project for your company. You are working you’re your project team to prepare for the qualitative risk analysis process. Mary, a project team member, does not understand why you need to complete qualitative risks analysis. You explain to Mary that qualitative risks analysis helps you determine which risks needs additional analysis. There are also some other benefits that qualitative risks analysis can do for the project. Which one of the following is NOT an accomplishment of the qualitative risk analysis process?
A. Cost of the risk impact if the risk event occurs
B. Corresponding impact on project objectives
C. Time frame for a risk response
D. Prioritization of identified risk events based on probability and impact
220-901 vce Correct Answer: A
QUESTION 83
Mark works as a Network Administrator for NetTech Inc. He wants users to access only those resources that are required for them. Which of the following access control models will he use?
A. Discretionary Access Control
B. Mandatory Access Control
C. Policy Access Control
D. Role-Based Access Control
Correct Answer: D
QUESTION NO: 84
Windows platform, the path when installing the software a lot, multi-path software LUN masked ghost, in the “Device Manager” to see if the disk drive less due to the redundant connections generated a
A. True
B. False
220-901 exam Answer: B
QUESTION NO: 85
UltraPath for Windows before installing the items you need to check what? (Choose three)
A. Check the operating system version and patch compatibility with UltraPath
B. Be sure to open HBA card comes with Failover and Failback Function
C. Check the Microsoft iSCSI Initiator installed a built-in multi- path driver
D. The old version is not installed on the application server to confirm UltraPath for Windows
Answer: A,C,D
QUESTION NO: 86
Upgrade for S2600 need to upgrade the controller software upgrade SES
A. True
B. False
220-901 dumps Answer: B
QUESTION NO: 87
About WWN: World Wide Name (WWN) is the only 128 addresses by the manufacturer embedded in each port.
A. True
B. False
Answer: B
QUESTION NO: 88
When installing UltraPath for Linux, prompted “the system is not supported by UltraPath driver, exit!!”, Requires:
A. Check the server operating system type and version is supported by multi- path software
B. Check the HBA card driver is supported by multi-path software
C. Check whether the software is open-iSCSI multipathing software support
D. None of the above comments
220-901 pdf Answer: A
We have been offering the best kind of customer services for our students as well so that when they wish to prepare for their CompTIA 220-901 dumps exam, they can talk to us with all of their queries that they have in their minds. “CompTIA A+ Certification Exam”, also known as 220-901 exam, is a CompTIA certification which covers all the knowledge points of the real CompTIA exam. Pass4itsure CompTIA https://www.pass4itsure.com/220-901.html dumps exam questions answers are updated (296 Q&As) are verified by experts. The associated certifications of 220-901 dumps is CompTIA A+.