If you want to succeed in the CompTIA PenTest + PT0-001 exam. I strongly recommend Pass4itsure PT0-001 exam study materials. https://www.pass4itsure.com/pt0-001.html This is related to the actual exam. After using Pass4itsure PT0-001 questions and answers, you will accept that it brings you closer to success. They have a 100% money-back guarantee.
Pass4itsure CompTIA PT0-001 PDF Dumps 2020
Pass4itsure PDF contains complete questions and answers that can guide you through 145 questions and answers to prepare for the PT0-001 exam. -PT0-001 exam resources:
CompTIA PT0-001 PDF Dumps https://drive.google.com/open?id=1rnx8enaNWU1JZgIXdwG86OduS5MFkqEf
Related Exam
- 220-1001 :CompTIA A+ Certification Exam: Core 1, 253 Q&As Updated: Apr 26, 2020
- 220-1002 :CompTIA A+ Certification Exam: Core 2, 303 Q&As Updated: Apr 27, 2020
- 220-301 :A+ CORE HARDWARE(2003 Objectives), 1760 Q&As Updated: May 02, 2020
- 220-302 :A+ OS TECHNOLOGY(2003 Objectives), 405 Q&As Updated: Apr 30, 2020
- 220-303 :A+ Core Hardware Exam -Arabic or Greak only, 105 Q&As Updated: Apr 30, 2020
- 220-304 :A+ Core OS Technologies Exam – Arabic or Greak only, 105 Q&As Updated: Apr 30, 2020
- 220-601 :CompTIA A+ Essentials 220-601 Exam, 99 Q&As Updated: May 02, 2020
- 220-602 :CompTIA A+ 220-602 Exam(IT Technician designation pathway), 1156 Q&As Updated: May 02, 2020
- 220-603 :CompTIA A+ 220-603(Remote Support Tech designation, 418 Q&As Updated: May 02, 2020
- 220-604 :CompTIA A+ 220-604 Exam(Depot Tech designation pathway), 275 Q&As Updated: Apr 27, 2020
- 220-611 :CompTIA A+ Essentials Exam – Arabic only, 105 Q&As Updated: Apr 30, 2020
- 220-612 :CompTIA A+ 220-612(IT Technician)Exam – Arabic only, 105 Q&As Updated: May 02, 2020
- 220-701 :CompTIA A+ Essentials (2009), 387 Q&As Updated: May 02, 2020, 220-702 :CompTIA A+ Practical Application (2009 Edition), 422 Q&As Updated: May 02, 2020
- 220-801 :CompTIA A+ Certification Exam, 1110 Q&As Updated: Apr 25, 2020
- 220-802 :CompTIA A+ Certification Exam, 993 Q&As Updated: Apr 29, 2020
- 220-901 :CompTIA A+ Certification Exam, 599 Q&As Updated: Apr 29, 2020
- 220-902 :CompTIA A+ Certification Exam, 1534 Q&As Updated: Apr 29, 2020
- 225-020 :CDIA+ CERTIFICATION EXAM-2002 OBJECTIVES, 143 Q&As Updated: May 01, 2020
- 225-030 :CDIA+ Certification, 255 Q&As Updated: Apr 30, 2020
- AD1-001 :CompTIA Mobile App Security+ Certification Beta Exam (Android Edition), 105 Q&As Updated: Apr 26, 2020
- ADR-001: CompTIA Mobile App Security+ Certification Exam (Android Edition), 102 Q&As Updated: Apr 27, 2020
- AOD-001: Accenture Intelligent Digital Platform (AIDP) Certification Exam, 105 Q&As Updated: May 02, 2020
- BR0-001 :CompTIA Bridge Exam – Security+, 150 Q&As Updated: May 02, 2020
Features of PT0-001 Study Material:
- All PT0-001 exam questions are updated on a regular basis.
- In case of the failure, you’ll get a full refund.
12% Off – Use Discount Coupon Code
Practice PT0-001 Exam Questions 1-13
If you want to practice CompTIA PT0-001 exam questions, then you can definitely use the help of PT0-001 practice exam questions. It provides you with a good opportunity to understand the weak points in your examination area. Get 700-760 new questions:
QUESTION 1
A penetration tester was able to retrieve the initial VPN user domain credentials by phishing a member of the IT
department. Afterward, the penetration tester obtained hashes over the VPN and easily cracked them using a dictionary
attack Which of the following remediation steps should be recommended? (Select THREE)
A. Mandate all employees take security awareness training
B. Implement two-factor authentication for remote access
C. Install an intrusion prevention system
D. Increase password complexity requirements
E. Install a security information event monitoring solution.
F. Prevent members of the IT department from interactively logging in as administrators
G. Upgrade the cipher suite used for the VPN solution
Correct Answer: ABD
QUESTION 2
Which of the following BEST explains why it is important to maintain confidentiality of any identified findings when
performing a penetration test?
A. Penetration test findings often contain company intellectual property
B. Penetration test findings could lead to consumer dissatisfaction if made pubic
C. Penetration test findings are legal documents containing privileged information
D. Penetration test findings can assist an attacker in compromising a system
Correct Answer: D
QUESTION 3
A security consultant receives a document outlining the scope of an upcoming penetration test. This document contains
IP addresses and times that each can be scanned. Which of the following would contain this information?
A. Rules of engagement
B. Request for proposal
C. Master service agreement
D. Business impact analysis
Correct Answer: A
QUESTION 4
After successfully capturing administrator credentials to a remote Windows machine, a penetration tester attempts to
access the system using PSExec but is denied permission. Which of the following shares must be accessible for a
successful PSExec connection?
A. IPCS and C$
B. C$ and ADMINS
C. SERVICES and ADMINS
D. ADMINS and IPCS
Correct Answer: B
QUESTION 5
Click the Exhibit button.
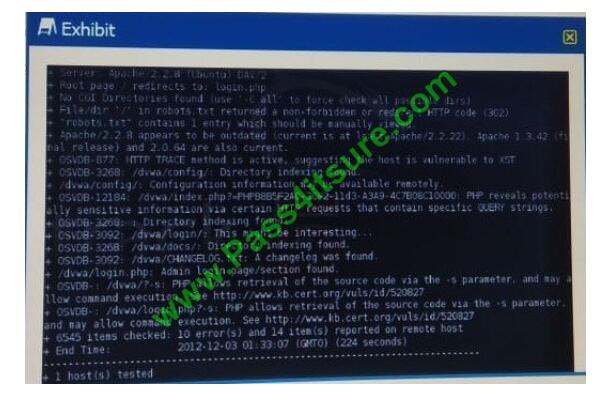
Given the Nikto vulnerability scan output shown in the exhibit, which of the following exploitation techniques might be
used to exploit the target system? (Select TWO)
A. Arbitrary code execution
B. Session hijacking
C. SQL injection
D. Login credential brute-forcing
E. Cross-site request forgery
Correct Answer: CD
QUESTION 6
A recently concluded penetration test revealed that a legacy web application is vulnerable lo SQL injection Research
indicates that completely remediating the vulnerability would require an architectural change, and the stakeholders are
not m a position to risk the availability of the application Under such circumstances, which of the following controls are
low-effort, short-term solutions to minimize the SQL injection risk? (Select TWO).
A. Identify and eliminate inline SQL statements from the code.
B. Identify and eliminate dynamic SQL from stored procedures.
C. Identify and sanitize all user inputs.
D. Use a whitelist approach for SQL statements.
E. Use a blacklist approach for SQL statements.
F. Identify the source of malicious input and block the IP address.
Correct Answer: DF
QUESTION 7
At the beginning of a penetration test, the tester finds a file that includes employee data, such as email addresses, work
phone numbers, computers names, and office locations. The file is hosted on a public web server. Which of the
following BEST describes the technique that was used to obtain this information?
A. Enumeration of services
B. OSINT gathering
C. Port scanning
D. Social engineering
Correct Answer: B
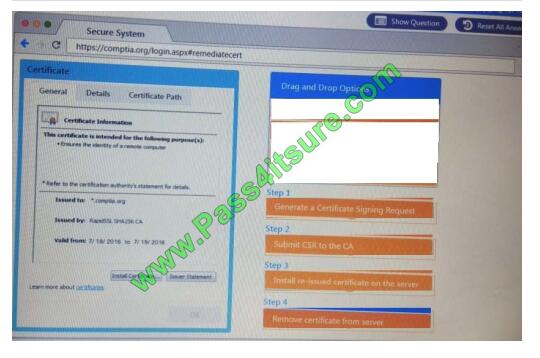
QUESTION 8
Performance based You are a penetration Inter reviewing a client\\’s website through a web browser.
Instructions:
Review all components of the website through the browser to determine if vulnerabilities are present.
Remediate ONLY the highest vulnerability from either the certificate source or cookies.
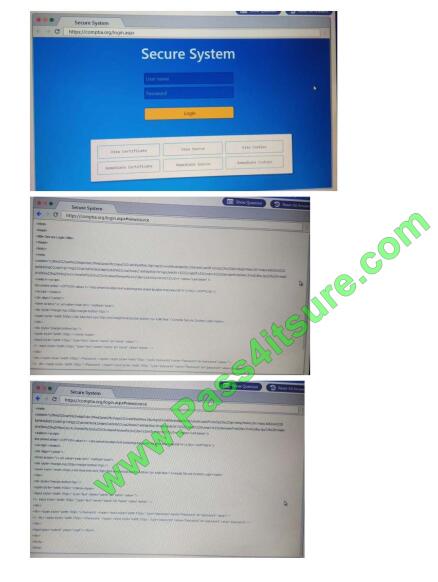
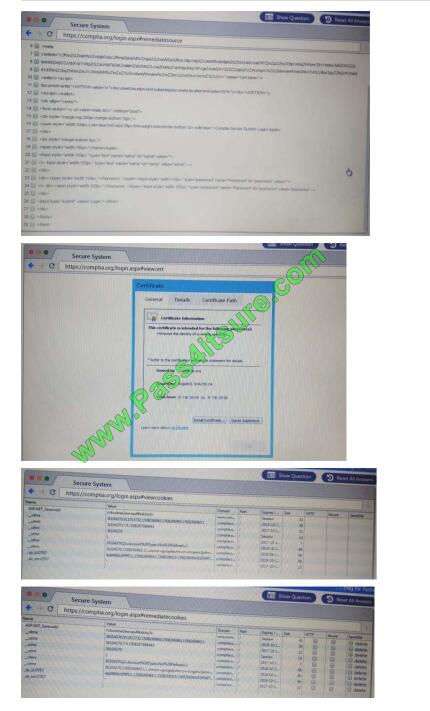
Select and Place:
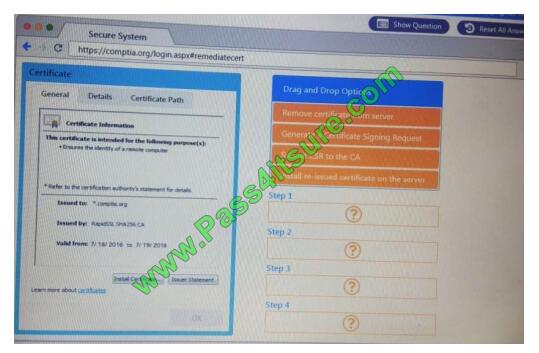
Correct Answer:
QUESTION 9
A penetration tester is performing a remote scan to determine if the server farm is compliant with the company\\’s
software baseline . Which of the following should the penetration tester perform to verify compliance with the baseline?
A. Discovery scan
B. Stealth scan
C. Full scan
D. Credentialed scan
Correct Answer: D
QUESTION 10
A penetration tester identifies the following findings during an external vulnerability scan:
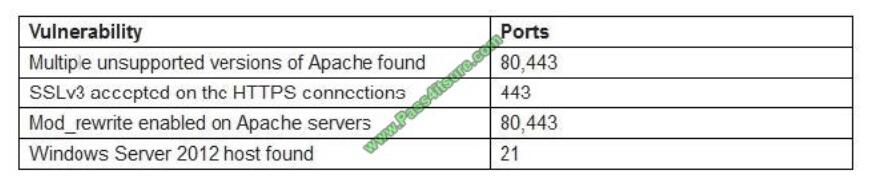
Which of the following attack strategies should be prioritized from the scan results above?
A. Obsolete software may contain exploitable components
B. Weak password management practices may be employed
C. Cryptographically weak protocols may be intercepted
D. Web server configurations may reveal sensitive information
Correct Answer: C
QUESTION 11
A penetration tester is in the process of writing a report that outlines the overall level of risk to operations. In which of the
following areas of the report should the penetration tester put this?
A. Appendices
B. Executive summary
C. Technical summary
D. Main body
Correct Answer: B
QUESTION 12
In a physical penetration testing scenario, the penetration tester obtains physical access to a laptop following potential
NEXT step to extract credentials from the device?
A. Brute force the user\\’s password.
B. Perform an ARP spoofing attack.
C. Leverage the BeEF framework to capture credentials.
D. Conduct LLMNR/NETBIOS-ns poisoning.
Correct Answer: A
QUESTION 13
A penetration tester wants to launch a graphic console window from a remotely compromised host with IP 10.0.0.20 and
display the terminal on the local computer with IP 192.168.1.10. Which of the following would accomplish this task?
A. From the remote computer, run the following commands: Export IHOST 192.168.1.10:0.0 xhost+ Terminal
B. From the local computer, run the following command ssh -L4444 : 127.0.01:6000 -% [email protected] xterm
C. From the local computer, run the following command ssh -r6000 : 127.0.01:4444 -p 6000 [email protected]
“xhost+; xterm”
D. From the local computer, run the following command Nc -1 -p 6000 Then, from the remote computer, run the
following command Xterm | nc 192.168.1.10 6000
Correct Answer: A
CompTIA PT0-001 PDF Dumps https://drive.google.com/open?id=1rnx8enaNWU1JZgIXdwG86OduS5MFkqEf
summarize:
If you are passionate about CompTIA experts in a certain way, the answer to all PT0-001 pdf questions will be your personal ideal choice.https://www.pass4itsure.com/pt0-001.html CompTIA PT0-001 dumps help a person master the complex topics in the exam questions.