The latest CompTIA Security+ SY0-501 exam Practice Questions and Answers
Security+ focuses on the latest trends and techniques in risk management, risk mitigation, threat management and intrusion detection. We share the latest effective CompTIA Security+ SY0-501 exam dumps online Practice test to improve your skills! You can also choose SY0-501 PDF! Get the full SY0-501 dumps: https://www.pass4itsure.com/sy0-501.html (Q&as:543) to pass the exam easily!
The CompTIA Security+ exam will certify the successful candidate has the knowledge and skills required to install and configure systems to secure applications, networks, and devices; perform threat analysis and respond with appropriate mitigation techniques; participate in risk mitigation activities; and operate with an awareness of applicable policies, laws, and regulations. The successful candidate will perform these tasks to support the principles of confidentiality, integrity, and availability.
[PDF] Free CompTIA Security+ SY0-501 pdf dumps download from Google Drive: https://drive.google.com/open?id=1xz8qeRFeSLig2DhPaltDQ1YoF3PWl_qy
[PDF] Free Full CompTIA pdf dumps download from Google Drive: https://drive.google.com/open?id=1SnVb1WLCtG5umIgtJ4zeNNSpuAFWZ3yg
CompTIA Security+ Certification – CompTIA IT Certifications: https://certification.comptia.org/certifications/security
Latest effective CompTIA Security+ SY0-501 Exam Practice Tests
QUESTION 1
A security administrator receives an alert from a third-party vendor that indicates a certificate that was installed in the
browser has been hijacked at the root of a small public CA. The security administrator knows there are at least four
different browsers in use on more than a thousand computers in the domain worldwide.
Which of the following solutions would be BEST for the security administrator to implement to most efficiently assist with
this issue?
A. SSL
B. CRL
C. PKI
D. ACL
Correct Answer: B
QUESTION 2
Which of the following would MOST likely appear in an uncredentialed vulnerability scan?
A. Self-signed certificates
B. Missing patches
C. Auditing parameters
D. Inactive local accounts
Correct Answer: D
QUESTION 3
Which of the following can be provided to an AAA system for the identification phase?
A. Username
B. Permissions
C. One-time token
D. Private certificate
Correct Answer: A
QUESTION 4
The SSID broadcast for a wireless router has been disabled but a network administrator notices that unauthorized users
are accessing the wireless network. The administer has determined that attackers are still able to detect the presence of
the wireless network despite the fact the SSID has been disabled.
Which of the following would further obscure the presence of the wireless network?
A. Upgrade the encryption to WPA or WPA2
B. Create a non-zero length SSID for the wireless router
C. Reroute wireless users to a honeypot
D. Disable responses to a broadcast probe request
Correct Answer: D
QUESTION 5
Which of the following cryptographic attacks would salting of passwords render ineffective?
A. Brute force
B. Dictionary
C. Rainbow tables
D. Birthday
Correct Answer: B
QUESTION 6
A security administrator suspects that a DDoS attack is affecting the DNS server The administrator accesses a
workstation with the hostname of workstation01 on the network and obtains the following output from the if config
command:
IP Address : 192.168.1.26 Subnet Mask : 255.255.255.0 Default Gateway : 192.168.1.254 DNS Server : 192.168.1.254
The administrator successfully pings the DNS server from the workstation. Which of the following commands should be
issued from the workstation to verify the DDoS attack is no longer occurring?
A. dig www.google.com
B. dig 192.168.1.254
C. dig workstationl.com
D. dig 192.168.1.26
Correct Answer: C
QUESTION 7
Ann, a security administrator, has been instructed to perform fuzz-based testing on the company\\’s applications.
Which of the following best describes what she will do?
A. Enter random or invalid data into the application in an attempt to cause it to fault
B. Work with the developers to eliminate horizontal privilege escalation opportunities
C. Test the applications for the existence of built-in- back doors left by the developers
D. Hash the application to verify it won\\’t cause a false positive on the HIPS.
Correct Answer: A
QUESTION 8
Which of the following would be MOST effective in reducing tailgating incidents?
A. Mantrap
B. Faraday cage
C. Motion detection
D. Bollards
Correct Answer: A
QUESTION 9
A security analyst captures forensic evidence from a potentially compromised system for further investigation. The
evidence is documented and securely stored to FIRST:
A. maintain the chain of custody.
B. preserve the data.
C. obtain a legal hold.
D. recover data at a later time.
Correct Answer: B
QUESTION 10
A network administrator wants to ensure that users do not connect any unauthorized devices to the company network.
Each desk needs to connect a VoIP phone and computer. Which of the following is the BEST way to accomplish this?
A. Enforce authentication for network devices
B. Configure the phones on one VLAN, and computers on another
C. Enable and configure port channels
D. Make users sign an Acceptable use Agreement
Correct Answer: A
QUESTION 11
Which of the following attack types BEST describes a client-side attack that is used to manipulate an HTML iframe with
JavaScript code via a web browser?
A. Buffer overflow
B. MITM
C. XSS
D. SQLi
Correct Answer: C
QUESTION 12
Which of the following are MOST susceptible to birthday attacks?
A. Hashed passwords
B. Digital certificates
C. Encryption passwords
D. One time passwords
Correct Answer: A
QUESTION 13
While working with a small, local farm to improve its security practices, a security consultant notices attempted logons to
the farm\\’s email server from a foreign country. The consultant can help block these attempts by implementing:
A. firewall ACLs.
B. port security.
C. an IDS.
D. A reverse proxy.
Correct Answer: D
CompTIA Security+ is the first security certification IT professionals should earn. It establishes the core knowledge required of any cybersecurity role and provides a springboard to intermediate-level cybersecurity jobs.
Share 13 of the latest CompTIA Security+ SY0-501 dumps Practice tests for free to help you improve your skills. SY0-501 PDF download Online! Get the full SY0-501 dumps: https://www.pass4itsure.com/sy0-501.html (Q&as:543). Easily pass the exam!
[PDF] Free CompTIA Security+ SY0-501 pdf dumps download from Google Drive: https://drive.google.com/open?id=1xz8qeRFeSLig2DhPaltDQ1YoF3PWl_qy
[PDF] Free Full CompTIA pdf dumps download from Google Drive: https://drive.google.com/open?id=1SnVb1WLCtG5umIgtJ4zeNNSpuAFWZ3yg
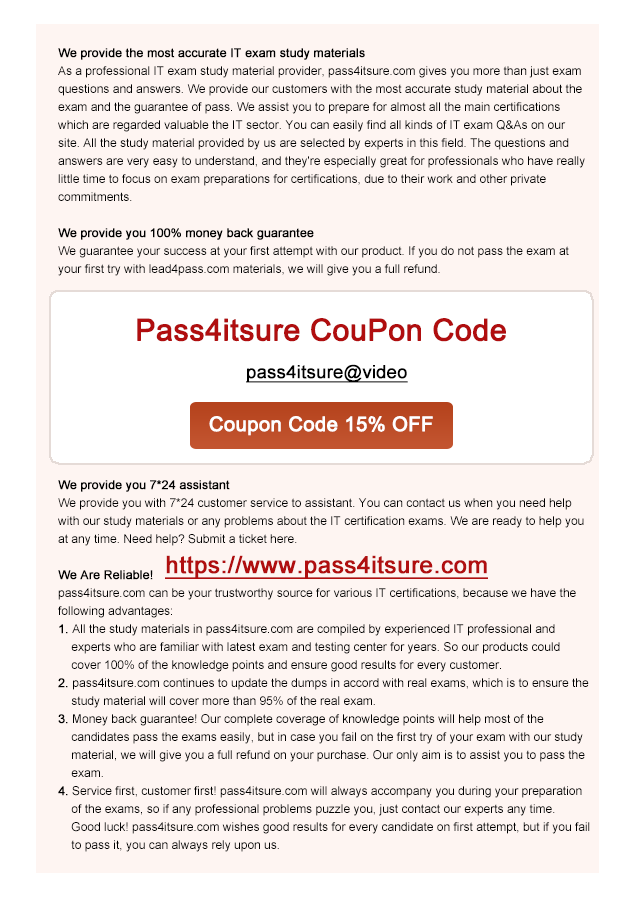
pass4itsure Promo Code 12% Off
related: https://www.certfans.com/valid-microsoft-70-473-dumps-study-guide/